Apple lets some Big Sur network traffic bypass firewalls
Enlarge (credit: Patrick Wardle)
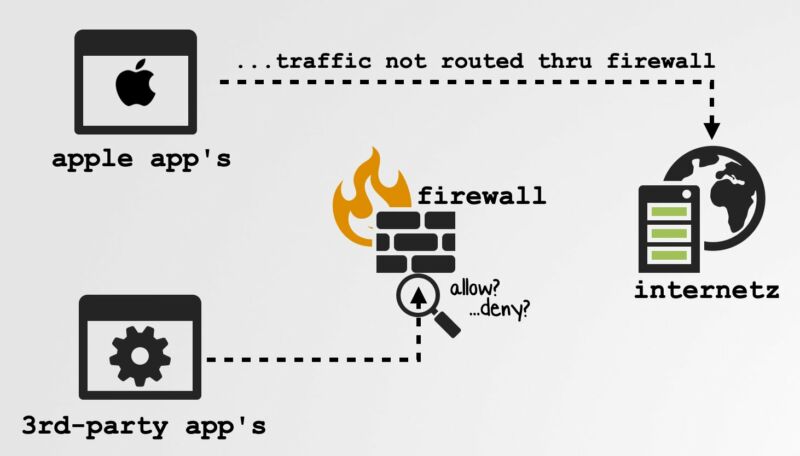
Firewalls aren’t just for corporate networks. Large numbers of security- or privacy-conscious people also use them to filter or redirect traffic flowing in and out of their computers. Apple recently made a major change to macOS that frustrates these efforts.
Beginning with macOS Catalina released last year, Apple added a list of 50 Apple-specific apps and processes that were to be exempted from firewalls like Little Snitch and Lulu. The undocumented exemption, which didn't take effect until firewalls were rewritten to implement changes in Big Sur, first came to light in October. Patrick Wardle, a security researcher at Mac and iOS enterprise developer Jamf, further documented the new behavior over the weekend.
In Big Sur Apple decided to exempt many of its apps from being routed thru the frameworks they now require 3rd-party firewalls to use (LuLu, Little Snitch, etc.)
— patrick wardle (@patrickwardle) November 14, 2020
Q: Could this be (ab)used by malware to also bypass such firewalls?
A: Apparently yes, and trivially sopic.twitter.com/CCNcnGPFIB
“100% blind”
To demonstrate the risks that come with this move, Wardle—a former hacker for the NSA—demonstrated how malware developers could exploit the change to make an end-run around a tried-and-true security measure. He set Lulu and Little Snitch to block all outgoing traffic on a Mac running Big Sur and then ran a small programming script that had exploit code interact with one of the apps that Apple exempted. The python script had no trouble reaching a command and control server he set up to simulate one commonly used by malware to exfiltrate sensitive data.
Read 9 remaining paragraphs | Comments
from Tech – Ars Technica https://ift.tt/3kH4j0o




Comments
Post a Comment