Buffer overruns, license violations, and bad code: FreeBSD 13’s close call
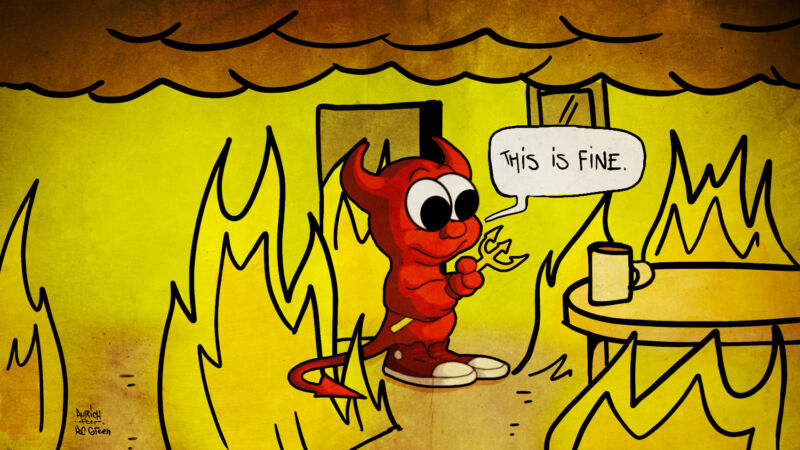
Enlarge / FreeBSD's core development team, for the most part, does not appear to see the need to update their review and approval procedures. (credit: Aurich Lawson (after KC Green))
At first glance, Matthew Macy seemed like a perfectly reasonable choice to port WireGuard into the FreeBSD kernel. WireGuard is an encrypted point-to-point tunneling protocol, part of what most people think of as a "VPN." FreeBSD is a Unix-like operating system that powers everything from Cisco and Juniper routers to Netflix's network stack, and Macy had plenty of experience on its dev team, including work on multiple network drivers.
So when Jim Thompson, the CEO of Netgate, which makes FreeBSD-powered routers, decided it was time for FreeBSD to enjoy the same level of in-kernel WireGuard support that Linux does, he reached out to offer Macy a contract. Macy would port WireGuard into the FreeBSD kernel, where Netgate could then use it in the company's popular pfSense router distribution. The contract was offered without deadlines or milestones; Macy was simply to get the job done on his own schedule.
With Macy's level of experience—with kernel coding and network stacks in particular—the project looked like a slam dunk. But things went awry almost immediately. WireGuard founding developer Jason Donenfeld didn't hear about the project until it surfaced on a FreeBSD mailing list, and Macy didn't seem interested in Donenfeld's assistance when offered. After roughly nine months of part-time development, Macy committed his port—largely unreviewed and inadequately tested—directly into the HEAD section of FreeBSD's code repository, where it was scheduled for incorporation into FreeBSD 13.0-RELEASE.
Read 61 remaining paragraphs | Comments
from Tech – Ars Technica https://ift.tt/3depci6
Comments
Post a Comment